
Honeypots: An Advanced Solution in IT Threat Detection
Publication Date: April 25, 2026
By Mark Ledman
Cybersecurity threats continue to evolve and broaden the threat landscape. In this time of artificial intelligent (AI) technology advancement, the threat actors, who used to be highly skilled technical people, are no longer dependent on advanced technical knowledge. Conversely, we have learned through the CrowdStrike Global Threat Report about organized threat actor organizations, their behaviors, and the types of cyberattacks they are involved in. The skills of some threat actors have increased to the level where think tank organizations are recognizing that some of the threat actors have the skills of data scientists.
During this time of change and advancement of generative and agentic AI and AI malware, many organizations are rethinking their security strategy. An important aspect of their security strategy, or security posture, is an improvement in their threat detection. If one layer of your organization’s defense strategy does not detect an attack, ideally another layer will.
Educause—a nonprofit association and large community of IT leaders—reports year-over-year growth in cyberattacks against higher education, with education now the most targeted sector globally. A topic that auditors should be asking their Chief Information Officer (CIO), Chief Information Security Officer (CISO), or Information Technology Security Officer (ITSO), is what changes or improvements are being made in their defense strategy as part of the changing cybersecurity threat landscape? Is your CIO considering using honeypots as part of their cybersecurity strategy?
The purpose of this article is to provide some information on a security tool and strategy that I have become familiar and intrigued with while observing a work team build and deploy a decoy network and series of honeypots. A honeypot can be used as a security mechanism to detect cyberattacks. Essentially, a honeypot is set up as a decoy to lure cyber attackers and detect, deflect, and study hacking attempts to gain unauthorized access to information systems. The results were immediate. In under eight minutes a newly deployed honeypot was experiencing threat activity. While I was impressed this activity happened very quickly, a security engineer informed me the average time for threat actor activity on a new honeypot is usually less than two minutes!
Honeypot Management Systems
A Honeypot Management System manages networks of honeypots and provides real-time data and real-time blocking of threat actors. Such a tool can leverage the strength of a consortium of colleges, universities, and other research institutions (collectively “Higher Ed”) that share real-time data with each other to block threat actors. For example, if a threat actor begins engaging with a honeypot on the West Coast, the moment the honeypot blocks the threat actor at the Higher Ed institution, the system immediately relays the threat intel to a central server. One can visualize this as a central hub with threat intel going to the hub and then relaying that same information simultaneously back out to the participating Higher Ed institutions blocking the threat actor IPs and Autonomous System Numbers (ASNs) in real time.
The education sector is now the most attacked industry globally, with institutions facing an average of 4,388 cyberattacks per week in 2025 [source:deepstrike.io]. One such Honeypot Management System, called STINGAR, purports to have over 100 participating Higher Ed organizations. Each organization identifies and blocks new IP addresses and ASNs and shares this information with other users to reduce the risk of their organizations being attacked and penetrated by known malicious actors. By collectively identifying and addressing threats, an institution on average could block half a million cyber threat actors per week using this security tool. That is potentially an average of over 20 million attacks per year!
Good questions to ask your CISO include: “What kind of policy or procedural enhancements are you making as a result of your alert or error analysis? How much time is being used to follow up on false positives? How much time is your security team working with the vendor to keep the solution up-to-date? The Honeypot Management System solution helps to check the boxes. Once the automated solution is set, there is minimal ITSO support required. From time to time, some higher ed organizations will move the various honeypots around to confuse or change the environment to provide a new look for a would-be threat actor. Honeypots can be deployed on-premise or in a cloud environment.
STINGAR was developed by the Security Operations Team at Duke University and provides this service to the higher ed community. The STINGAR website includes information about the product plus statistical information compiled from their threat detection system. The system gathers various types of threat data such as threats from other countries. A map of the globe is on the website that provides data points where the threat activity is coming from and a list of top countries by malicious IPs and number of ASNs.
How Honeypots Work
The following is a graphic to understand just how a decoy network with honeypots might look within a typical university network.
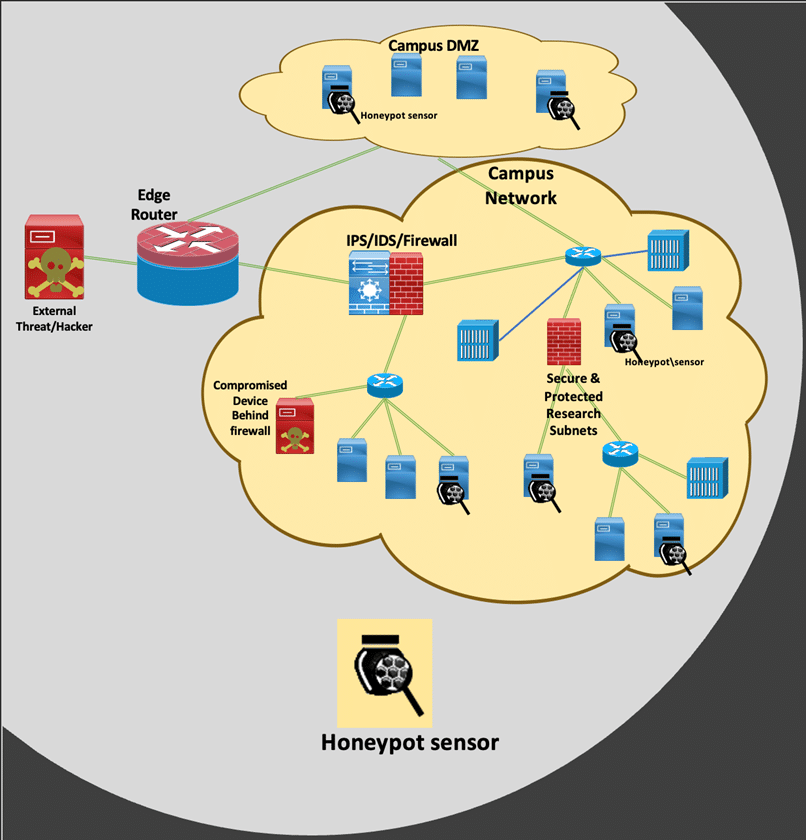
Honeypot diagram provided by STINGAR Team, IT Security Office, Duke University
A typical enterprise network connects to the Internet through a high-speed wide area network (WAN) via an edge router. Incoming data packets from the Internet are first processed by this router, which then forwards the packets into the internal enterprise network. These packets are typically inspected by a dedicated security system known as a firewall(or, more broadly, an intrusion detection or prevention system, IDS/IPS).
The firewall applies a set of predefined rules to evaluate incoming traffic, filtering out packets that match known malicious patterns or signatures. Packets identified as harmful are discarded (“dropped”), while the remaining traffic is allowed to proceed. However, not all malicious activity is easily identifiable—many attacker packets appear benign and do not match known signatures. As a result, a significant portion of potentially harmful traffic can pass through to internal network segments (such as Finance, Legal, Human Resources, Engineering, and the Registrar) and ultimately reach enterprise systems, including email and web servers, databases, user devices, and other connected equipment.
To address this limitation, organizations deploy honeypots—specialized systems designed to detect and study malicious activity. Honeypots are typically installed on a small number of systems within the network and function as controlled decoys (see image with honeypot magnifying glass for example). They are intentionally configured to appear vulnerable, thereby attracting attackers who are scanning for weaknesses.
When an attacker interacts with a honeypot—such as attempting to access a simulated service, exploiting a perceived vulnerability, or installing malicious software—the activity is immediately detected and recorded. This information is then transmitted to the honeypot management platform.
The platform aggregates this data and updates a “blocklist,” which is a continuously maintained list of identified malicious sources. This blocklist is automatically distributed to network enforcement points such as firewalls and edge routers. Once updated, these systems can identify and block any subsequent traffic originating from those malicious sources, preventing further access to the enterprise network.
This detection and response occurs automatically within seconds. From the attacker’s perspective, the enterprise network may appear to become unreachable, effectively cutting off further interaction.
In practice, this approach can significantly reduce malicious traffic within the network—often by a factor of 10 to 100 times. Under certain high-volume attack conditions, such as distributed denial-of-service (DDoS) events, reductions can be even greater, with the system blocking extremely large volumes of unwanted traffic. This both helps protect enterprise assets while allowing normal network operations to continue without manual intervention.
So, what does it take to build these honeypots? There are a couple of ways they can be built. At Duke University, STINGAR was first introduced in 2016, and has been in use for the past 10 years to protect Duke’s network. The people that are managing these have learned many of the behaviors and activities the cyber threat actors use. One way to build a honeypot is for your team of security architects and software engineers to build these from the ground up. Another way is to use an AI-agent tool to build the honeypot for you. The AI-agent tool includes an AI-agent for quality assurance to ensure your build is according to business needs and specifications.
There are many different types of honeypots, and each type will have a different profile visible to the attacker and mimic different behaviors of computer resources they represent, and each has a different level of allowable interaction with the threat actor before the trap is sprung. Once the honeypot is deployed, attack analysis reports are available in real time and brute force attacks on the network will be identified.
Conclusion
There is a continuous virtual arms race between the attackers using various threat exploits and the network defense teams. Attackers are continuously looking for different types of targets and data. AI-powered bots are scanning for high value research or user credentials, attempting to run cryptocurrency mining code on university CPU & GPU hardware assets, and other malicious scenarios. Honeypot management systems provide a live dashboard report indicating these attacks and where they came from in real time while blocking the source of the attacks to prevent further impact.
About the Author

Mark Ledman, CPA, CISA is an IT Audit Manager with Duke University. Mark has over 30 years of health care, government, and higher education audit experience. He has served on the board for Association of Healthcare Internal Auditors (AHIA) and Institute of Internal Auditors (IIA) committees. Mark serves on the ACUA Advocacy Committee as the strategic partner liaison with ISACA and has presented at three ACUA conferences. Mark serves on the ISACA IT Audit and Advisory Committee and as a reviewer for select ISACA IT publications, such as the recently published ITAF Framework.
